Die souveräne Europäische Supply Chain in der Software-Entwicklung

In today’s fast-paced software world, we often rely on complex supply chains and external services. But what happens when these dependencies turn into uncontrollable risks? This blog post highlights the importance of digital sovereignty in software development and shows how we, as developers and companies, can regain control over our value chain.
This provocative question illustrates the core problem: our supply chains are fragile. Dependencies on external providers are not just technical annoyances but symptoms of a deeper issue—we have relinquished control. Failures can occur anytime and unexpectedly, and the ability to respond quickly and autonomously is crucial for business continuity.
Our Chrome Catastrophe: A Wake-Up Call
A striking example of the pitfalls of external dependencies was an unexpected Chrome bug. A seemingly minor update to a browser used by millions caused massive problems in our applications. This dramatically demonstrated how quickly external factors can cripple our business processes, even when we ourselves made no mistakes.
The Invisible Threads: When Providers Change the Rules
Sometimes failures are not technical but strategic. Providers can change their business models, prices, or terms of use, which can have far-reaching consequences for dependent companies. Here are some examples:
-
Reddit (July 2023): Drastic changes to API pricing and rate limits led to the shutdown of many popular third-party apps as their operating costs skyrocketed.
-
VMWare (May 2025): After Broadcom acquired VMware, European customers faced extreme price increases of up to 1,500%, which industry analysts and EU associations say threaten the existence of many companies.
-
Hypothetical (2026): Imagine the US government banning access to services from Microsoft, AWS, Google, Oracle, Facebook, OpenAI, Anthropic for companies in the EU. Although fictional, this scenario highlights potential geopolitical risks.
These examples show that dependencies on external providers carry not only technical but also strategic and political risks. Digital sovereignty means minimizing these risks and retaining control over your own digital future.
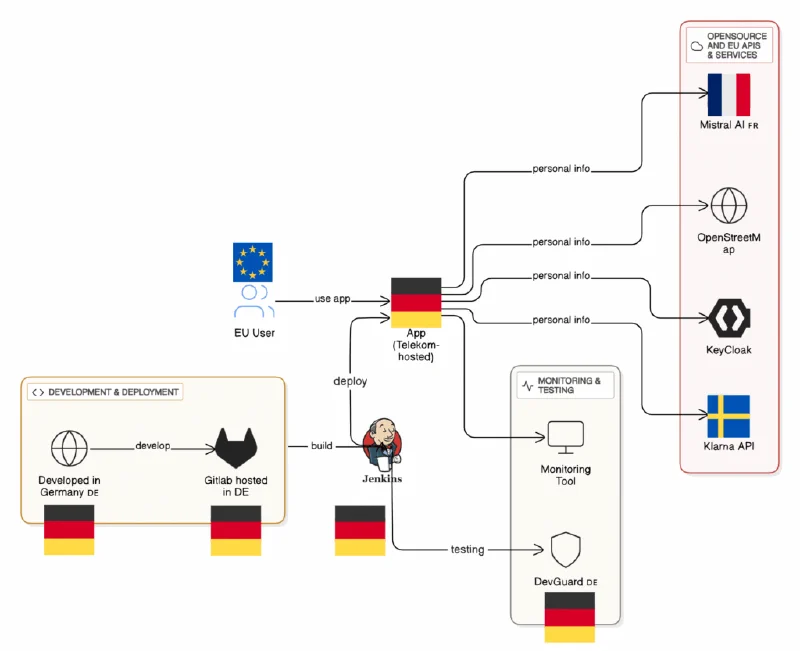
The Journey of Our Code: A Value Chain
Every software goes through a complex journey from idea to production. This “toolchain” consists of numerous stages where our code is processed, tested, built, and deployed. Dependencies can arise at each stage that affect our sovereignty. It is essential to analyze this value chain carefully and identify critical points.
Typical US Hyperscaler Architecture: Convenience with Compromises
Many companies rely on major US hyperscalers like AWS, Azure, or GCP. These undeniably offer convenience, scalability, and a wide range of services. However, this convenience often comes at a price: relinquishing control and creating dependencies that can prove risky in the long term. Data sovereignty, legal frameworks (such as the CLOUD Act), and the risk of vendor lock-in are key concerns here.
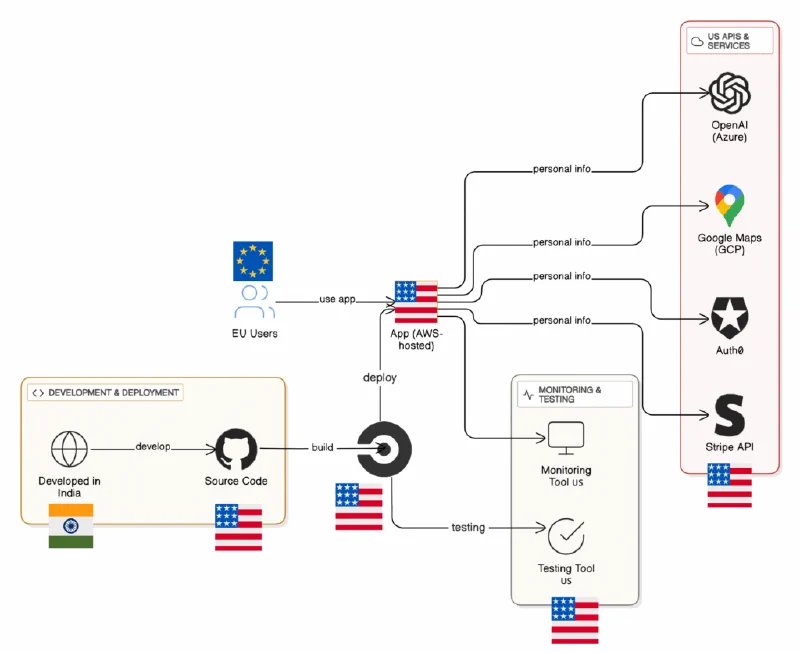
Station 1: The Code & Dependencies – Where Is Our Source Code Management System?
The place where our source code is managed is fundamental. Much of the world uses GitHub, a Microsoft (USA) platform. However, storing sensitive corporate data and intellectual property on servers outside one’s own jurisdiction carries risks.
The Standard
GitHub (Microsoft, USA)
The Sovereign Alternative
-
Self-Hosting: Solutions like GitLab or Gitea enable full control over your codebase and data.
-
European Hosts: Using SCM services from European providers ensures your data is subject to European data protection laws.
Station 2: The CI/CD Pipeline – Who Builds and Tests Our Code?
The Continuous Integration/Continuous Delivery (CI/CD) pipeline is the heart of modern software development. It automates building, testing, and deploying code. External CI/CD services like GitHub Actions or CircleCI are convenient but can also create dependencies.
The Standard
GitHub Actions, CircleCI
The Sovereign Alternative
-
Integrated Solutions: GitLab or Gitea offer their own integrated CI/CD features directly connected to your self-hosted code repository.
-
The Classic: Jenkins remains a robust and flexible open-source option for pipeline automation.
-
Use of Dependency Proxies: These help reduce reliance on external package repositories and increase control over your software supply chain.
-
Open Source Security Scanning: Tools like DevGuard enable early detection and remediation of security vulnerabilities in your dependencies without sending data to third parties.
Station 3: The Cloud Platform – On Whose Computers Does Our Application Ultimately Run?
Choosing the cloud platform is one of the most important decisions for digital sovereignty. The major US hyperscalers dominate the market, but their services are often subject to US laws that may allow data access even outside the USA.
The Standard
AWS, Azure, GCP
The Sovereign Alternative
-
European Providers: Companies like Open Telekom Cloud, STACKIT, Hetzner, OVHcloud, or Scaleway offer cloud services subject to European data protection standards and operate data centers in Europe.
-
The Foundation: OpenStack and Kubernetes are open-source technologies that enable building and operating your own cloud infrastructure, ensuring maximum control and independence.
Station 4: Managed Services & APIs – To Whom Do We Give Our Users’ Data?
Managed services and external APIs are convenient but mean relinquishing control over certain data or functionalities to third parties. This can range from authentication services to payment processors.
The Standard
Auth0 (IAM), Stripe / Paypal (Payment), Google Maps (Location)
The Sovereign Alternative
-
Open Source: For Identity and Access Management (IAM), Keycloak offers a powerful open-source solution. In payments, European providers like Klarna or Adyen exist, and for location services, OpenStreetMap is an excellent open-source alternative to Google Maps.
-
European SaaS Providers: Many European companies offer specialized Software-as-a-Service (SaaS) solutions compliant with European data protection regulations.
Station 5: AI Tools & Assistants – The Smart Colleague: Who Owns Your Prompt?
The rise of AI tools and assistants like ChatGPT or GitHub Copilot is revolutionizing software development. However, using these services raises important questions about data sovereignty. Your code and prompts could be used as training data on external servers, often outside EU jurisdiction.
The Standard
ChatGPT, Claude, Gemini, IDEs like Windsurf, Cursor, GitHub Copilot.
Risk: Your code & prompts as training data on US servers.
Risk: OpenAI may not delete temporary chats upon request.
The Sovereign Alternative
-
European Models: Promising European AI models like Mistral (Le Chat, API), Teuken, Aleph Alpha (PhariaAI), or Flux (image generation) are developed and operated within the EU.
-
Open-Source Models for Maximum Self-Hosting: Models like Mistral (EU), GPT-OSS (new, OpenAI), Llama (Meta US, LLAMA-4 not EU), Deepseek, Qwen (China), or Gemma (Google) can be self-hosted, providing maximum control over your data and its use.
Trade-off: Peak performance vs. 100% control. The decision depends on data sensitivity and desired sovereignty level.
Station 6: Outsourcing – Whom Do We Trust to Develop Software for Our Business-Critical Processes?
Outsourcing is common to reduce costs or access specialized knowledge. However, the choice of outsourcing partner and their location directly impacts digital sovereignty, especially regarding data protection and compliance.
The Standard Reflex
Outsourcing to Asia/Eastern Europe
Risk: GDPR is often not mandatory outside the EU and is frequently misunderstood or poorly implemented in third countries.
Additionally: NIS2, WCAG 2.1 (Web Content Accessibility Guidelines), AI Act—the list of compliance requirements is growing, making outsourcing outside the EU more complex and risky.
The Sovereign Alternative
Collaboration with partners within the EU under the same legal framework. This ensures not only GDPR compliance but also better understanding and easier implementation of other European regulations.
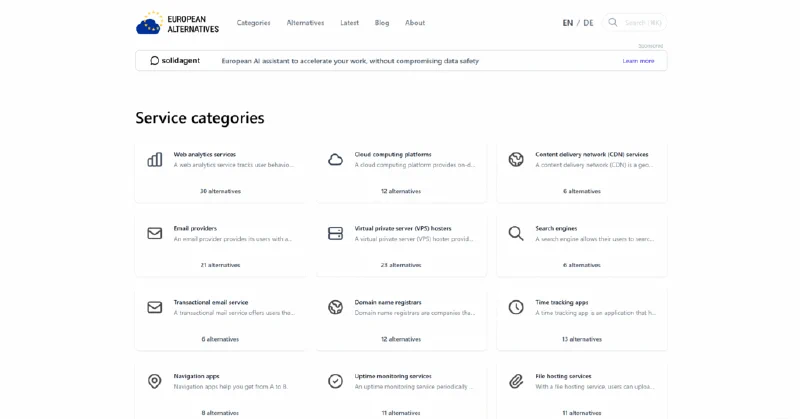
European Alternatives: A Growing Movement
The good news is that a growing movement toward greater digital sovereignty is emerging in Europe. More and more European companies and open-source projects offer powerful and privacy-friendly alternatives to established US providers. It is worthwhile to actively explore and support these options.
Why the “Effort”? Control, Data Protection, and a Strong Ecosystem
Switching to sovereign solutions may seem like an “effort” at first glance. But the benefits far outweigh the costs in the long run:
-
Control & Resilience: You retain full control over your data, infrastructure, and processes, increasing your company’s resilience against external shocks.
-
Data Protection & Security: Compliance with European data protection standards like GDPR is simplified, and your sensitive data is better protected.
-
Strong Local Ecosystem: You strengthen the European tech landscape and foster innovation within the EU.
It’s Not About Protectionism. It’s About Options and Conscious Decisions.
Digital sovereignty is not a call for protectionism or isolationism. It’s about making informed choices, understanding dependencies, and having options. It may be a long path, but every step counts. If we don’t start, we won’t arrive.
Convenience and Speed vs. Control and Security
Choosing digital sovereignty often means balancing convenience and speed on one side with control and security on the other. The major hyperscalers undeniably offer fast deployment and easy scalability. But for business-critical applications and sensitive data, long-term control and security should take priority.

Your git commit for Sovereignty: Practical Steps for Developers
As developers, we play a key role in shaping digital sovereignty. Every single “git commit” can make a difference. Here are practical steps you can take:
$ Ask: Is there an open-source alternative? From the EU?
$ Question defaults: Don’t blindly choose the hyperscaler.
$ Start small: Host your own GitLab runner or files with an EU provider.
$ Share knowledge & contribute: Submit a pull request to an EU project.
$ Use IaC: Provider-independent, reproducible, and automated—multi-cloud with e.g. Terraform.
$ Run dual tracks: Build fallback options.
